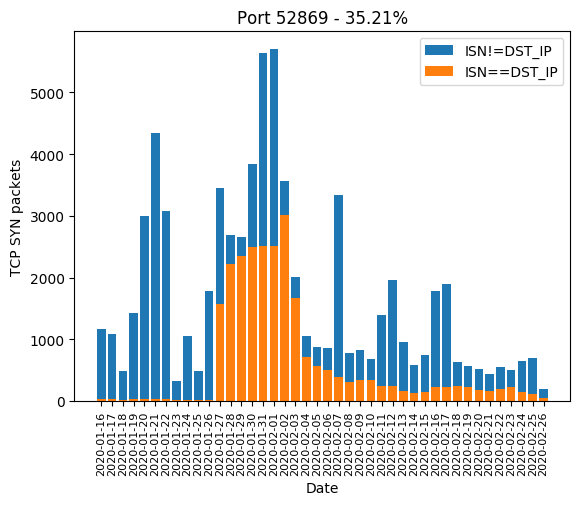
When Cameras and Routers attack Phones. Spike in CVE-2014-8361 Exploits Against Port 52869 - SANS Internet Storm Center

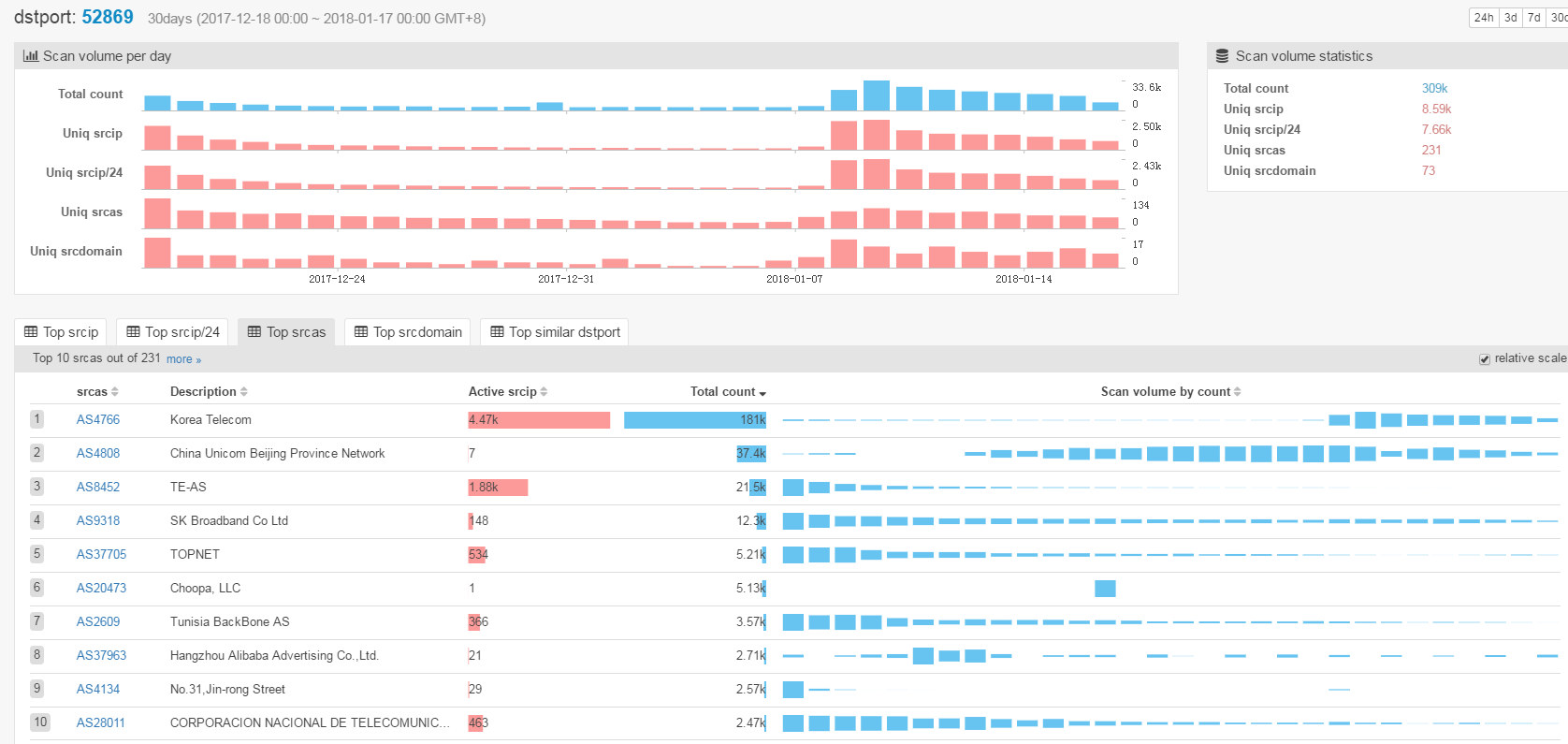
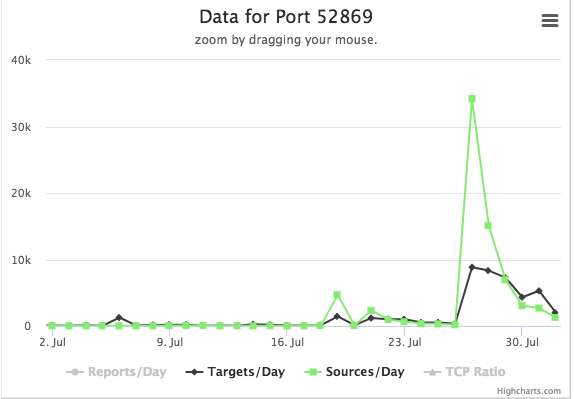
Masafumi Negishi on Twitter: "Another moobot variant has been scanning 9530/tcp since May 25, mostly infected in Japan. The threat actor exploited CVE-2014-8361 on 52869/tcp. Many home routers in Japan remain vulnerable